Sub-Second Defense: Why Flowtriq is the New Standard for DDoS Mitigation
When your server dies under a thunder of bogus SYNs: why detection speed and clean mitigation matter
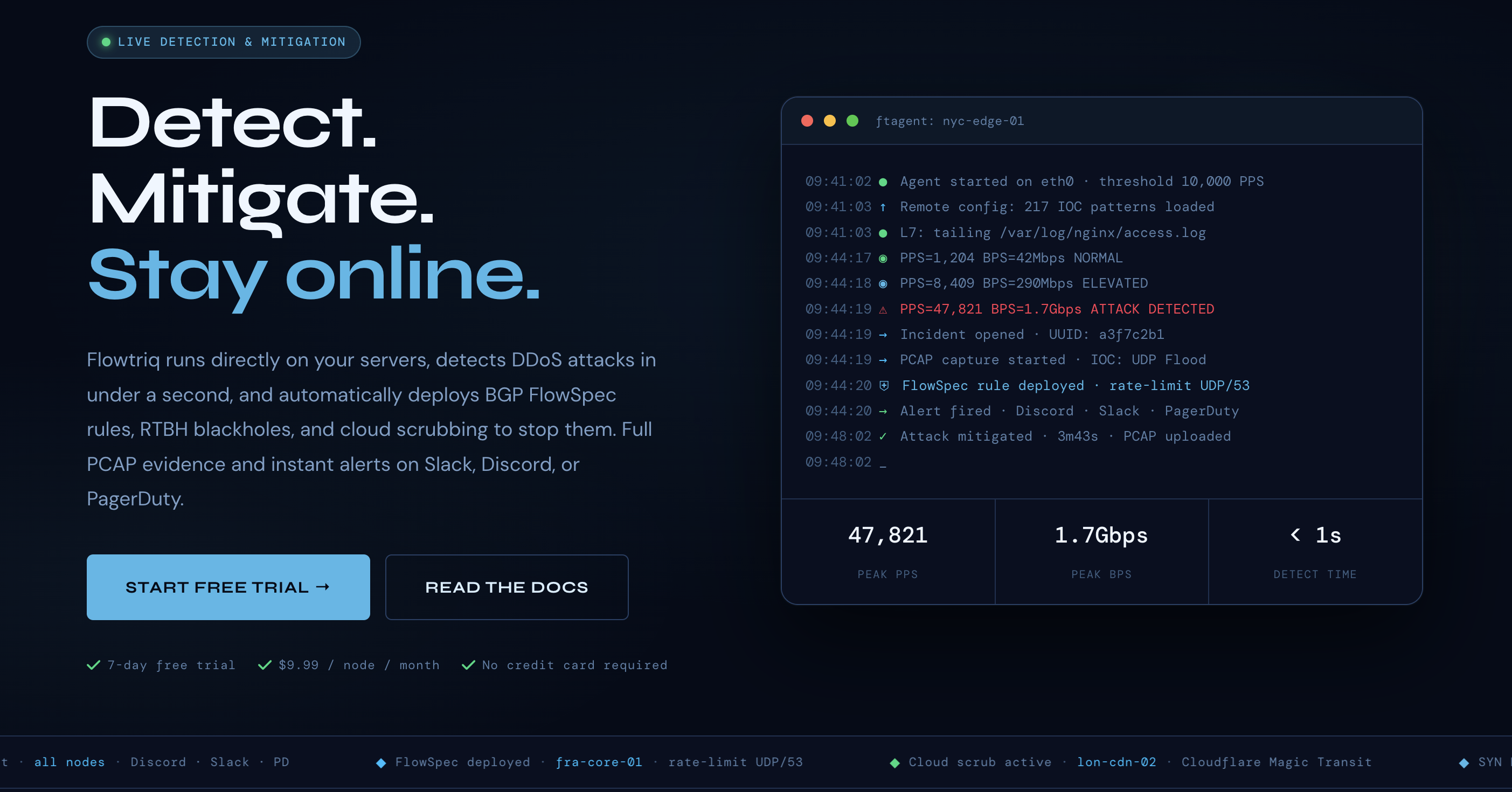
You know the drill—latency spikes, player disconnects, frantic Slack pings, and a billing surprise from a scrubbing vendor. Flowtriq’s pitch is simple and visceral: detect and mitigate DDoS before users notice. Built as a lightweight Python agent (ftagent) that reads packets directly from the NIC and pairs with a cloud dashboard, Flowtriq focuses on sub-second anomaly detection, automated escalation to BGP FlowSpec/RTBH or cloud scrubbing, and on-demand full PCAP capture for forensics. The design philosophy prioritizes local, low-latency telemetry, automated response playbooks, and forensic preservation — a practical stack for hosting providers, game servers, and edge operators who need surgical, fast defenses.
Architecture & Design Principles
Flowtriq is agent-first: a small ftagent installs on Linux servers (<2 minutes) and performs packet-level telemetry. The agent likely leverages libpcap/AF_PACKET or raw-socket capture for per-packet PPS/flow metrics while maintaining a low CPU footprint. Telemetry and alerts are sent to a multitenant cloud control plane that stores baselines, IOC databases, and audit logs. Key design decisions: local baseline learning (adaptive thresholds checked every second), immutable audit trails, and automated mitigation orchestration (BGP FlowSpec/RTBH announcements or upstream scrubbing). Scalability is horizontal — multi-node management via a single dashboard plus cloud-native event handling for high concurrency. The stack balances on-host visibility with centralized coordination, reducing time-to-mitigation without shipping terabytes of telemetry continuously.
Feature Breakdown
Core Capabilities
- ▸ Sub-second detection & classification: FTAgent computes PPS and flow fingerprints per second and classifies 8+ attack types (SYN, UDP, DNS/amplification, HTTP floods, ICMP, memcached, L7). Use case: a sudden SYN spike triggers a SYN-flood signature within <1s and a preconfigured FlowSpec rule.
- ▸ Auto-mitigation orchestration: On detection, escalation policies can deploy BGP FlowSpec rules, RTBH blackholes, or hand off traffic to scrubbing providers (Cloudflare, OVH, Hetzner). Use case: escalate local mitigations first, then auto-route to Magic Transit when volume exceeds upstream capacity.
- ▸ Forensics & IOC correlation: automatic full-PCAP capture on every attack, correlated against a 642k+ IOC library (Mirai variants included). Use case: reproduce multi-vector attacks post-event and attribute botnet signatures for takedown or customer reporting.
Integration Ecosystem
Flowtriq offers webhook-first alerting and multi-channel notifications (Discord, Slack, PagerDuty, OpsGenie, SMS, email). It integrates with BGP peers for FlowSpec and RTBH (automating route announcements), and supports cloud scrubbing APIs for Cloudflare Magic Transit and major scrubbing centers. A Python agent enables local scripting and rudimentary customization; webhooks allow SIEM/automation chains. The platform’s audit log and status pages facilitate customer communications and incident transparency.
Security & Compliance
Data handling centers on ephemeral telemetry with optional long-term PCAP retention for enterprises (365 days). Immutable audit logs and playbook traces support post-incident compliance. Flowtriq publishes original research (e.g., Mirai kill switch, CVE-2024-45163) and offers certifications — useful signals for maturity, though specific ISO/SOC attestations aren’t listed publicly.
Performance Considerations
Detection latency is a core metric: PPS checks every second enable sub-second classification and mitigation initiation. Because the agent performs packet capture locally, network overhead to the cloud is minimized; however, capture and on-host analysis impose CPU and NIC load — typically modest for modern instances but measurable under high-throughput conditions. The platform avoids traffic-based pricing ($9.99/node/month), which simplifies economics for bursty environments.
How It Compares Technically
Flowtriq is an agent‑centric, hybrid defense: compare this with edge/scrubbing-first vendors such as Cloudflare Magic Transit (edge scrubbing + global anycast), AWS Shield Advanced (cloud-native, API-driven protections), and appliance/ISP solutions like Netscout/Arbor or Radware. Flowtriq excels in rapid local detection and orchestration to upstream mitigations, whereas Cloudflare/AWS provide massive global scrubbing capacity but rely on upstream routing changes. For technical buyers:
- ▸ If you need per-node, sub-second on-host visibility → Flowtriq.
- ▸ If you need global anycast scrubbing at scale → Cloudflare Magic Transit (https://www.cloudflare.com/products/magic-transit/) or Akamai/Prolexic (https://www.akamai.com).
- ▸ If you are an ISP requiring network-level scrubbing appliances → Netscout/Arbor (https://www.netscout.com) or Radware (https://www.radware.com).
Developer Experience
The ftagent is Python-based, which lowers the barrier for customization and rapid debugging. Flowtriq exposes webhooks and probably REST APIs for orchestration; documentation quality is supported by free tools (BGP FlowSpec builder, PCAP analyzer) and published research. The platform’s certification courses and active tooling suggest good knowledge transfer and community trust — helpful for smaller teams without dedicated security ops.
Technical Verdict
Flowtriq’s strength is speed-to-action: on-host packet telemetry, adaptive baselines, and automated playbooks that move from detection to mitigations (FlowSpec/RTBH/scrubbing) in under a second. It’s ideal for hosting providers, game hosts, ISPs, and SaaS platforms that need per-node granularity without heavy traffic billing. Limitations: reliance on agent installation (not suitable for purely edge-first architectures) and the usual tradeoffs of on-host capture (CPU/I/O overhead, retention costs). In short, for startups and operators who must "detect locally, mitigate smartly, and document everything," Flowtriq is a pragmatic, evidence-driven option. The data shows it’s built for fast, automated defense rather than replacing global scrubbing incumbents.